Tech Support Scams Attack? No Worry!
The most prominent internet scam is the technical support scam, where scammers create a false virus scare to trick victims into buying fake advice, but Qiling Backup can secure your data, protecting you from losing it to such scams.
What Are Tech Support Scams?
Tech support scams start with scammers pretending to offer genuine technical support, often at a lower cost than what's available elsewhere. They aim to trick victims into believing they can resolve their technical issues, only to extract money or sensitive information.
Scammers use various tactics to deceive people, including calls, texts, and error messages. These communications often contain a phone number and request that you call it, which can lead to the scammer extracting your balance or gaining access to your phone. The different methods used for these frauds are constantly evolving.
Scammers use various tactics, including emails with links to websites, to trick people into sharing personal info or data. These emails often seem legitimate and may include links to fake helplines that are actually scams.
Using public Wi-Fi can lead to financial losses and personal data theft. Scammers may initiate a virus on your device, claiming it was already present, and then hack into your system with a single click, compromising your sensitive information.
How to Identify and Act Against Tech Support Scams
Staying vigilant is key to identifying tech support scams and protecting yourself from financial and data losses. By recognizing the differences between legitimate and fraudulent tech support, you can avoid falling victim to these scams and keep your money and data safe.
Pop-Ups
The most common way to scam someone is often a pop-up warning on the screen, disguised as a message from a legitimate source or your phone, or even a warning about viruses or errors.
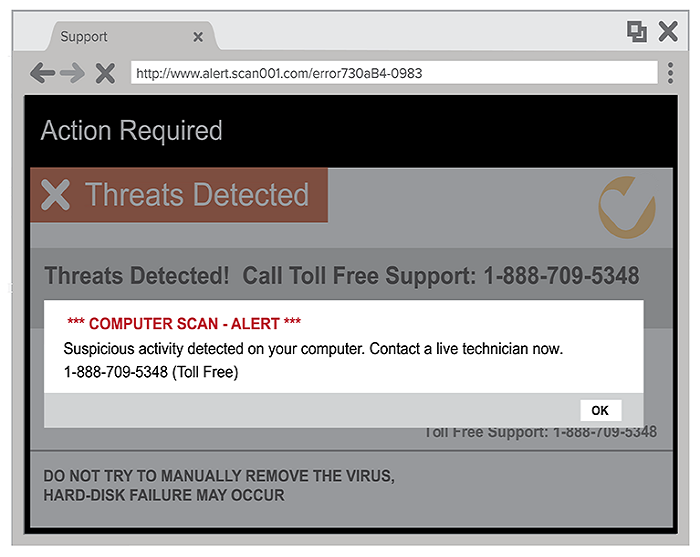
If you get this kind of pop-A pop-up window on your computer may ask you to contact a specific number for technical support. However, it's generally safer to ignore such pop-ups and instead contact the company's official customer support through their website or a trusted contact method. This can help prevent potential security risks and ensure you receive accurate and reliable assistance.
Calls
You may receive a suspicious call from a phone number that appears to be from a well-known company. The caller claims to be from a reputable organization, often mentioning issues with your computer or a hidden virus. This is a common tactic used by scammers to trick you into believing they are legitimate. Be cautious and do not fall for their tricks.
Cut off Scam Call:Don't answer calls from unknown numbers or unexpected calls, as they may be scams. If someone claims there's a problem with your computer that you're not aware of, hang up immediately and don't pay any bills for services you didn't request. Be cautious and protect yourself.
Online Ads
When seeking technical support, it's best to contact reliable companies directly rather than searching online and potentially falling victim to scams. Stick to trusted companies with a strong online presence and positive reviews on social media and search engines to ensure you get genuine assistance.
Never Make the Transaction: Try not to make transactions with your bank account without verifying the service. In case you do pay a scammer like that, call the helpline to your bank immediately. Inform them about all the details and ask if they can stop the transaction made or reverse any changes made if possible.
Does Backup Protect Against Ransomware? Why Ask
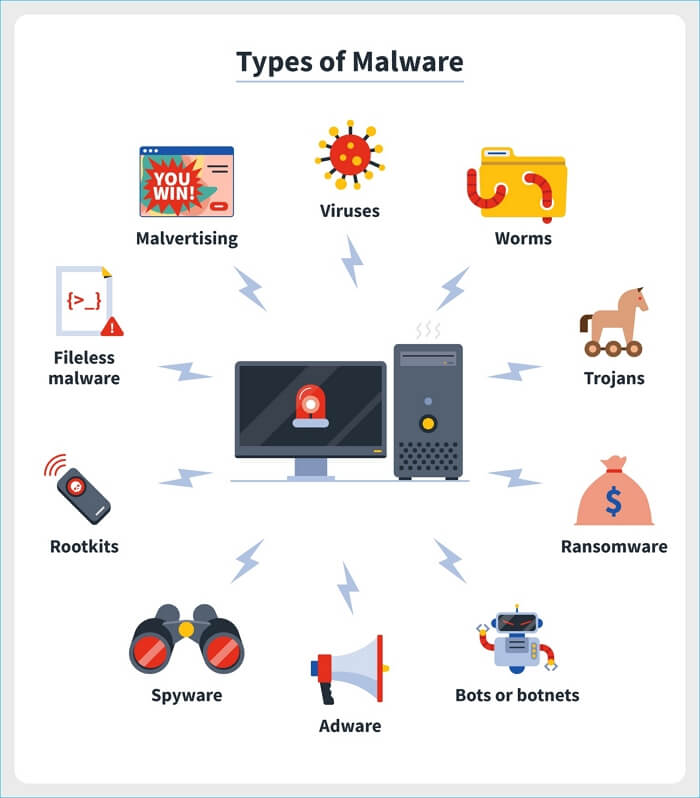
A computer backup can protect against ransomware by serving as a data prevention measure for disasters, including malware attacks, allowing a reliable backup service provider to safeguard against ransomware.
Tips To Prevent Tech Support Scams
To avoid falling victim to scams, it's essential to stay vigilant and aware of the tactics scammers use. Be cautious of unsolicited offers, especially those that seem too good to be true, and never provide personal or financial information to unknown individuals or entities.
1. Hyperlinks and Phone numbers
Be cautious with links and phone numbers received from unknown sources, such as forwarded messages, online ads, or spam emails, and avoid calling numbers provided by these sources.
2. Sharing Information
Be cautious and do not share your passwords, private data, or sensitive information with anyone, including your banking details, social media usernames, social security number, address, and date of birth, as this information is not typically required for technical support.
3. Caller ID
To avoid scams, consider using a caller ID to verify the caller's number. Scammers can easily spoof phone numbers, making it difficult to distinguish genuine calls from fake ones. Additionally, be cautious of unexpected calls and verify the caller's identity before engaging with them. Trustable sources typically have official company phone numbers and will inform you of any important updates.
4. Bank Transfers
To avoid using your bank account to pay for services, consider using cash or alternative payment methods like sending money via post or using gift cards, especially if you're not fully trusting the support you're receiving.
5. Suspicious Messages
Delete and block sources of spam texts. Report the email or phone number to the authorities. Take no action.
See More: Use Qiling Backup to Protect Yourself
Once a computer is infected with malware or ransomware, users lose access to their own data, with hackers often demanding high ransoms in exchange for its recovery, and even then, there's no guarantee the data will be restored.
With Qiling Backup, you can create a secure zone where viruses can't invade, protecting your backups from ransomware threats.
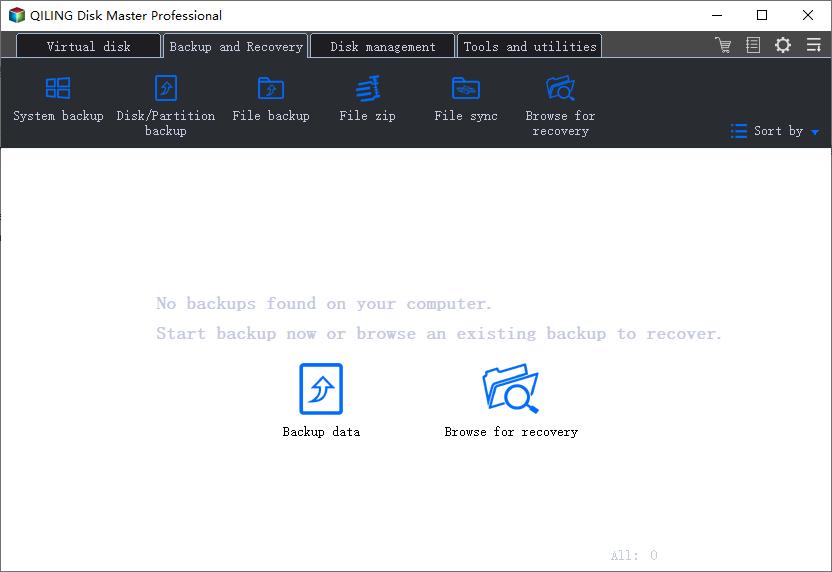
Follow the below steps to start the process:
Step 1. Launch Qiling Backup on your computer, and click System Backup on the Backup and recovery page.
Step 2.Your Windows operating system information and system related files and partitions will be automatically selected, so no manual selection is needed at this step. Next, you'll need to choose a location to save the system image backup by clicking on the illustrated area.
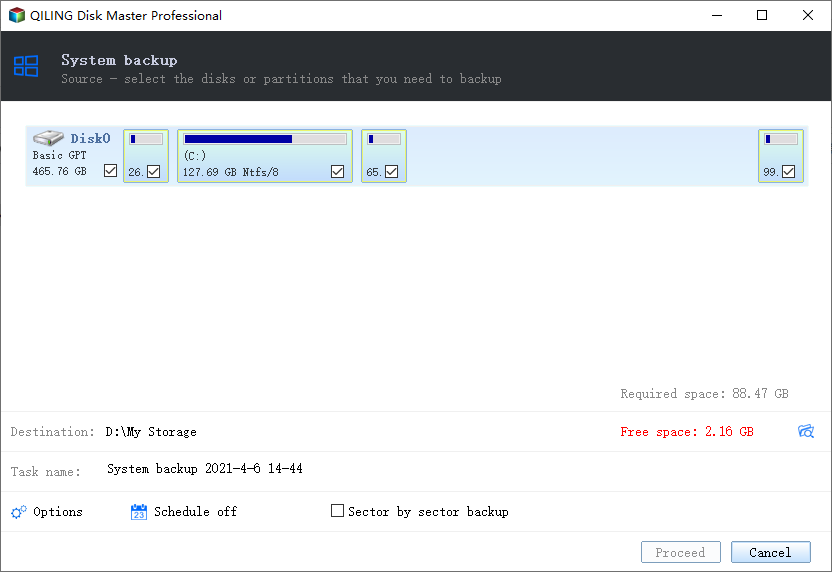
Step 3. The backup location can be another local drive on your computer, an external hard drive, network, cloud, or NAS. It's generally recommended to use an external physical drive or cloud to preserve system backup files.
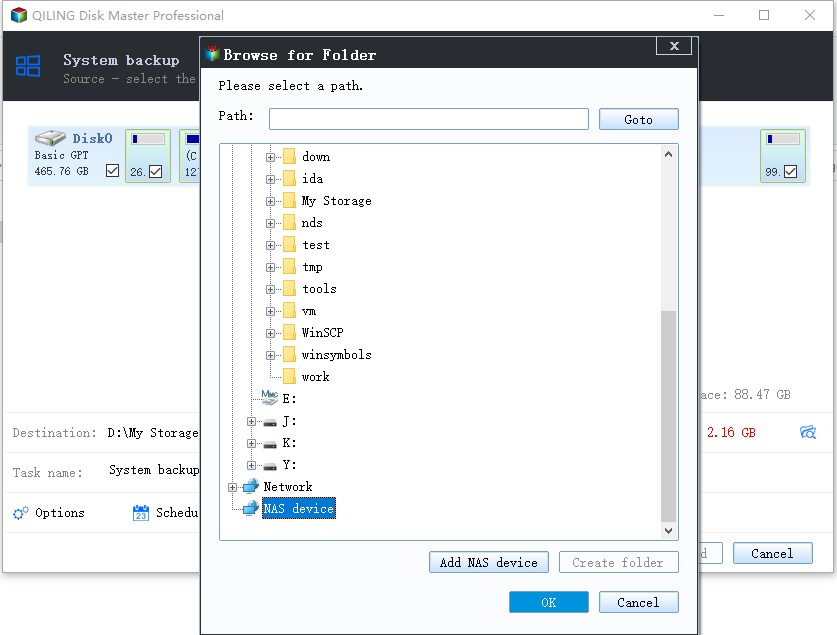
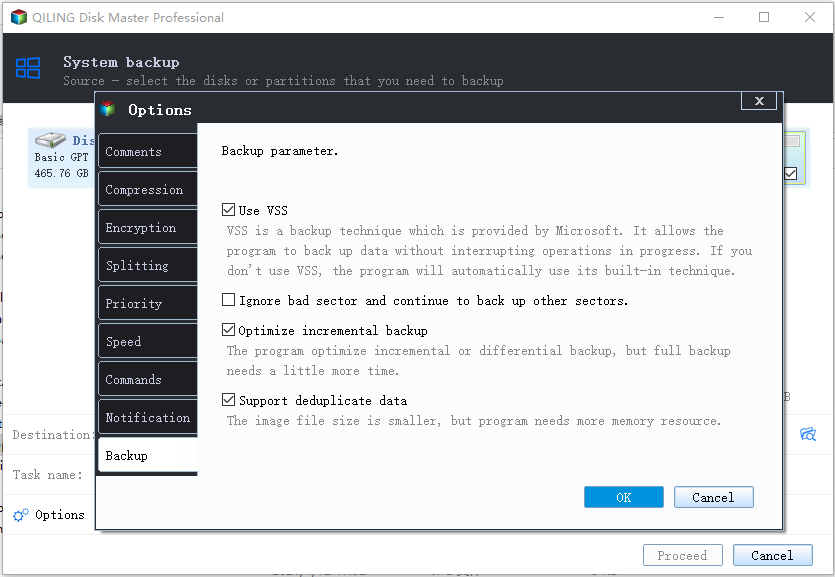
Step 4. Customization settings like enabling an automatic backup schedule in daily, weekly, monthly, or upon an event, and making a differential and incremental backup are available in the Options button. If interested, click "Proceed" and the Windows system backup process will begin. The completed backup task will display on the left side in a card style.
Conclusion
To avoid falling victim to tech support scams, remember to stay vigilant when online and keep the provided tips in mind. As cybercrimes continue to rise, it's essential to be aware of scammers' tactics. To minimize the risk of data loss, consider downloading Qiling Backup, which can not only migrate OS to an external HDD/SSD but also encrypt backups, providing an added layer of protection.
Related Articles
- 2022: How to Installl Windows 11 on M.2 SSD (with Pictures)
- How to Backup Microsoft Office Before Reformatting Hard Drive or PC
- Which One to Choose: What is the Best Gaming Laptop?
- Everything About S Mode in Windows 11
- How to Backup NAS? Top 3 Strategies
To back up your NAS, you have three options. You can simply copy your NAS data to an external hard drive, use backup software to securely transfer your files, or back up your NAS to a cloud drive for remote access and protection. - Backup Options in Windows 10: Which Is The Best Choice?
This article provides an in-depth look at the various Windows 10 backup options, comparing each one to help you determine the best choice for your needs. By the end of this article, you'll have a clear understanding of the different backup options available and be able to make an informed decision about which one to use.